 HP Inc.’s cybersecurity predictions for 2021 show the ripple effect of COVID-19 is likely to continue, leading to a rise in thread hijacking, whaling and human-operated ransomware
HP Inc.’s cybersecurity predictions for 2021 show the ripple effect of COVID-19 is likely to continue, leading to a rise in thread hijacking, whaling and human-operated ransomware
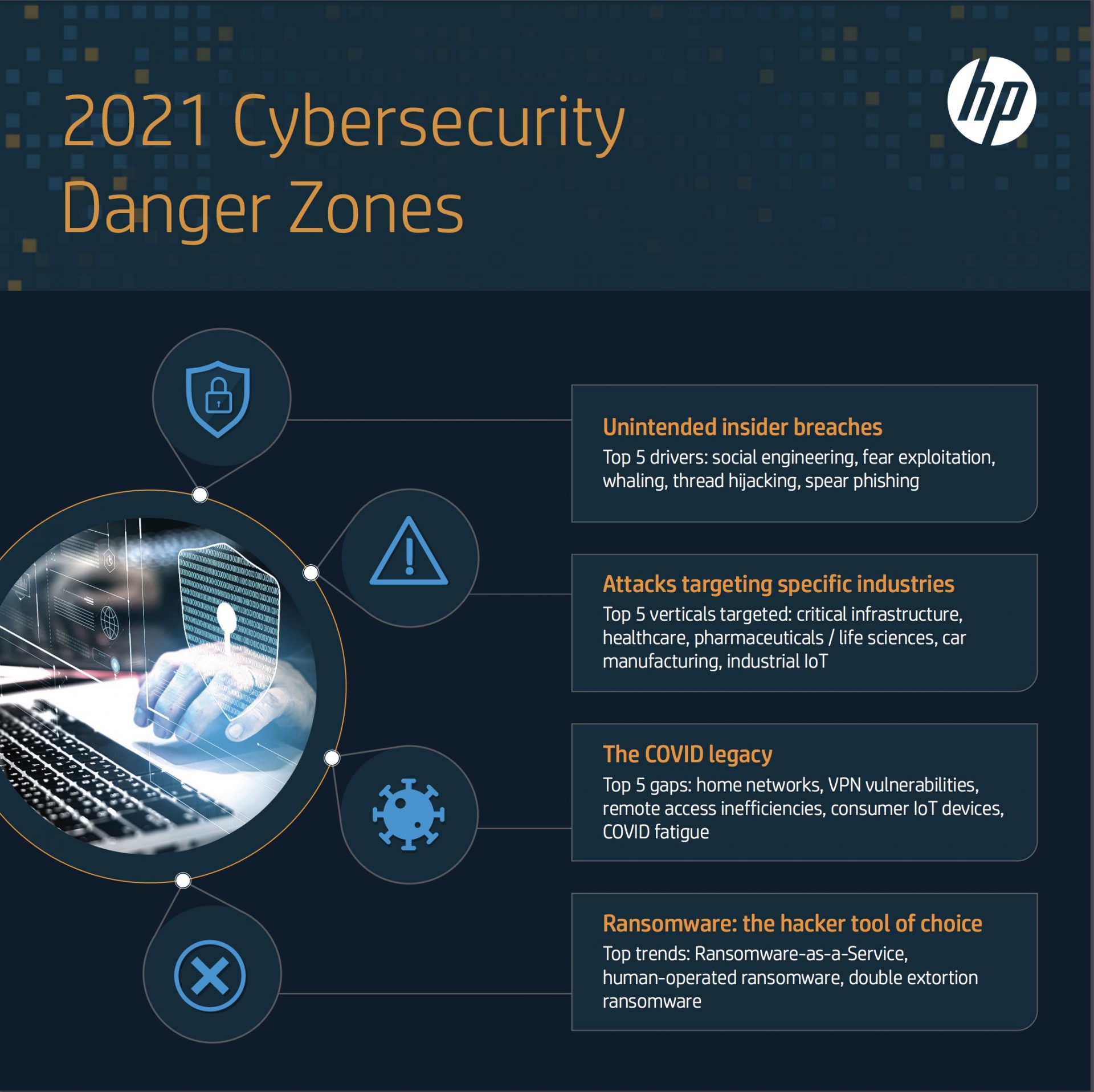
HP released its 2021 predictions on how security threats, such as human-operated ransomware, thread hijacking, unintentional insider threats, business email compromise and whaling attacks, are set to increase in the next 12 months.
HP’s cybersecurity experts including, Julia Voo, Global Lead Cybersecurity and Tech Policy; Joanna Burkey, CISO; Boris Balacheff, Chief Technologist for Security Research and Innovation at HP Labs; Dr. Ian Pratt, Global Head of Security for Personal Systems; and Alex Holland, Senior Malware Analyst,and experts from HP’s Security Advisory Board, Justine Bone, CEO at MedSec; and Robert Masse, Partner at Deloitte, all gave their predictions for the year ahead.
The dramatic changes to how we work in 2020 and the shift to remote working will continue to create challenges, said Julia Voo: “COVID-19 has weakened organisational security. Remote access inefficiencies, VPN vulnerabilities and a shortage of staff that can help the business adapt means data is now less secure.” From a cybercriminal’s perspective, the attack surface is widening, creating more opportunities, as Joanna Burkey explained: “We can expect to see hackers identifying and taking advantage of any holes in processes that were created, and still exist, after everyone left the office.”
Boris Balacheff pointed out that this also means that home devices will be under increased pressure: “We have to expect home infrastructure will be increasingly targeted. The scale at which we operate from home increases the incentive for attackers to go after consumer IoT devices and pivot to business devices on the same networks. And as we know, if attackers are successful with destructive attacks on home devices, remote workers won’t get the luxury of having someone from IT turning up at their door to help remediate the problem.”
Burkey also believes there will be more unintentional insider threats: “With employees working remotely, the lines between work and personal equipment are blurred, and innocent actions – such as reading personal email on a company machine – can have serious consequences.” Overall, the pandemic has increased the risk of employees making errors, as Robert Masse explains: “If you view the pandemic as a war experience, then organisations will be dealing with employee burnout. This can lead to an increased risk of errors in judgement.”
Ransomware has become the cybercriminal’s tool of choice, and this is likely to continue in the year ahead, commented Burkey: “What we’ll see is a rise in ransomware-as-service attacks where the threat is no longer the ‘kidnapping’ of data – it’s the public release of the data.”
The rise of ransomware has fuelled the growth of an ecosystem of criminal actors who specialise in different capabilities needed to pull off successful attacks. Malware delivered by email, such as Emotet, TrickBot and Dridex, are often a precursor to human-operated ransomware attacks. “To maximise the impact of an attack, threat actors use their access to compromised systems to deepen their foothold into a victims’ networks. Many crews use offensive security tools to gain control of a victim’s domain controllers, which are often the best point in a network to deploy ransomware,” explained Dr. Ian Pratt.
This trend is of particular concern to those in the public sector, as Alex Holland explains: “The rise of ‘double extortion’ ransomware, where victim data is exfiltrated before being encrypted, will particularly hurt public sector organizations, who process all manner of personally identifiable information. Even if a ransom is paid, there is no guarantee that a threat actor won’t later monetise the stolen data.”
In 2021, there will be more innovative phishing lures designed to trick users and make attacks harder to identify. “The most innovative mass phishing technique we see is email thread hijacking, which is used by the Emotet botnet. The technique automates the creation of spear-phishing lures by stealing email data from compromised systems. This data is then used to reply to conversations with messages containing malware, making them appear very convincing,” explained Dr. Ian Pratt. We can also expect to see more of these attacks targeting individuals working remotely, said Justine Bone: “Thanks to everything relying on strong authentication, as opposed to in-person presence, there is more opportunity for hackers to engage in social engineering to trick employees into divulging credentials.”
The prospect of continued social isolation has encouraged people to share more personal information online, which cybercriminals can weaponise. “Whaling, a form of highly targeted phishing attack aimed at senior executives, will become more prominent with cybercriminals able to take personal information shared online to build convincing lures leading to business email compromise fraud,” commented Masse. Many of these phishing emails will continue to exploit people through fear, according to Voo. “New fears will be used to drive people to open malicious emails – whether it’s COVID vaccines, financial concerns related to the lockdown and any political instability.”
Hackers will tailor attacks to target specific verticals – in particular, critical infrastructure, pharma and healthcare, Industrial IoT and education
One of the most at-risk verticals in 2021 will be healthcare. “Healthcare has been a perfect target – society depends on it and these organisations are typically under-resourced, change-averse and slow to innovate. Education also fits this criterion and could be another prime target,” said Bone. However, this threat extends beyond hospitals and doctor’s surgeries into more critical areas. “Due to the race to develop a new vaccine, pharmaceutical companies and research facilities will also continue to face adverse risk,” commented Masse.
But the next 12 months will also see other targets come into consideration for hackers. “Car makers, particularly EV companies, will become bigger targets as they grow in prestige and profitability, and we can also expect to see critical infrastructure and the Industrial Internet of Things continue to be in hackers’ crosshairs,” explained Masse.
Zero trust as a concept is not new, but the increase in remote working means that it is now a reality that organisations need to accept. “The traditional ways of securing access to the corporate network, applications and data are no longer fit for purpose. The perimeter has become obsolete. Over the years the workforce has become more dispersed, and SaaS adoption has risen – this means critical data is being hosted outside the enterprise firewall. The time has come for organizations to start protecting against the unknown, which means utilising zero trust, but in a way that is transparent to the user,” commented Pratt.
COVID-19 will be a key driver behind zero trust adoption and also means we’ll see greater innovation in this area. “Zero trust is the best defensive approach for enabling remote working, but for identity and access management to be seamless it needs to be easy to use. Quality authentication methods are a key enabler of zero trust, which is why technologies such as biometrics will be expected by end users in the future,” commented Bone.
“2020 demonstrated that is has become critical to manage highly distributed endpoint infrastructure,” commented Balacheff. “Organisations need to accept that the future is distributed. Everything from remote workers’ devices to industrial IoT devices have become the new frontlines of the cybersecurity battleground in our increasingly cyber-physical world. To meet this challenge, organisations need to re-think their security architectures and controls, and embrace the necessary innovation in technology and processes to help them support this new environment. For example, modern hardware technology exists that can help not only protect but also recover employees remotely and securely in the face of destructive attacks like those we have seen in the last few years.”
“Organisations face a huge security challenge in the year ahead, with cybercriminals becoming savvier about how to extract the most value out of victims,” comments Pratt. “Relying on detection alone will only result in an unsatisfactory outcome for the organization, so a more architecturally robust approach to security is required; one that builds protection in from the hardware up. Hardware-enforced technologies like micro-virtualisation are transparent to the end user – this means they can click on email attachments and download files as they normally would but are safe in the knowledge that if anything is malicious, it is rendered harmless. This protection-first approach leaves hackers with nothing to steal and no way to persist, helping organisations to deal with the variety of threats 2021 and beyond will throw at them.”